The Streisand Effect, for those not aware, is where an attempt to remove, hide, or censor a piece of information has the unintended consequence of publicizing that information more widely by way of drawing attention to it. It is named after Barbara Streisand, who once filed a lawsuit to have an arial image of her home removed from the Internet. In her case, it resulted in a flood of publicity and thousands of people viewing that image.
What happened here?
An individual took issue with a post that I wrote 8 years ago. The identity of the person and the content of the post aren’t relevant to this post, but what is important is that prior to this event, the post was sitting by itself, pretty much left alone except for for the occasional web crawler visiting it. The post would have stayed that way, except that the person who had an issue with my post decided to complain in a heavily trafficked forum. This resulted in the post receiving more traffic than the previous several months combined. Additionally, many more people were made aware of the contents of the post, which I’m fairly sure the person complaining did not want to see happen.
How about some numbers?
Here’s a graph of HTTP requests to that page over time:
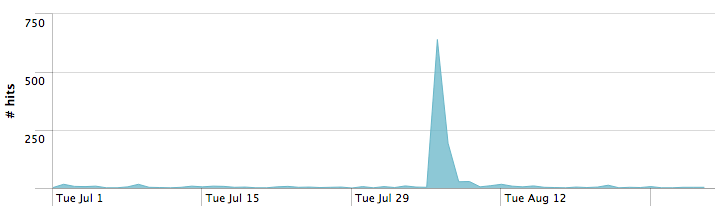
Note the huge spike, when is when the post in question was mentioned. Approximately one thousand separate people visited the post in question during the spike in traffic.
Now, what did we learn?
